Duplicate Records Incident Response for Hiring Systems
A compliance-first operating model to stop identity drift before it becomes an audit finding or a fraud pathway.
Duplicate candidate records are not a data hygiene issue. They are an identity control failure.Back to all posts
Real hiring problem: duplicates become an audit and fraud event
Duplicate candidate records across sourcing tools, ATS, and interview platforms create identity drift that breaks audit defensibility and opens a lane for proxy interviews. Compliance risk surfaces when Legal asks you to prove who approved a candidate and you cannot retrieve one coherent evidence trail because rubrics, verification outcomes, and timestamps are split across multiple profiles. Industry data indicates fraud is not rare in remote hiring pipelines, so treating duplicates as a cosmetic CRM problem creates avoidable legal exposure and mis-hire risk.
One person appears as three profiles across CRM, ATS, and interview platform due to email changes and forwarded invites.
Two different rubrics are scored on two different profiles, and the offer is approved on a third record.
A post-hoc reconstruction becomes the only way to answer who approved what, when.
Why legacy tools fail to stop identity drift
Legacy ATS, background check, and interview vendors optimize for their own transaction, not for a shared identity control plane. The result is sequential checks, missing event logs, and no SLA-bound merge governance. Without unified evidence packs and ATS-anchored audit trails, merges are handled in shadow workflows. That is an integrity liability because decisions become hard to defend under audit.
Waterfall sequencing that delays verification until late stages.
Vendor-specific IDs with no canonical candidate key.
No idempotency strategy for retries and out-of-order webhooks.
Rubrics stored per tool, not per candidate identity.
No merge SLAs, so duplicates persist until someone complains.
Ownership and accountability matrix
Assigning ownership is the control. If nobody owns merges and identity drift, duplicates will be handled in spreadsheets and DMs. Make sources of truth explicit: ATS for lifecycle state, verification evidence pack for identity assertions, interview platform as a consumer gated by identity state.
Recruiting Ops owns workflow, merge queue operations, and data quality enforcement.
Security owns identity policy, access control, and audit policy.
Hiring Managers own rubric discipline and resolving conflicting assessments.
Analytics owns dashboards, time-to-event metrics, and reconciliation reporting.
Modern operating model: instrumented identity and merge control
Treat hiring like secure access management: identity gate before access, event-based triggers, and evidence-first merges. Design for reconciliation. Webhooks arrive out of order, vendors create partial records, and candidates legitimately change emails. Deterministic identifiers and append-only logging are what keep the system defensible.
Identity verification before interview access for risk-tiered roles.
Event-based orchestration with idempotency keys for create, update, merge events.
Automated evidence capture for every merge decision and exception.
Dashboards for duplicate rate, time-to-merge, and SLA breach alerts.
Standardized rubrics tied to candidate key, written back into ATS.
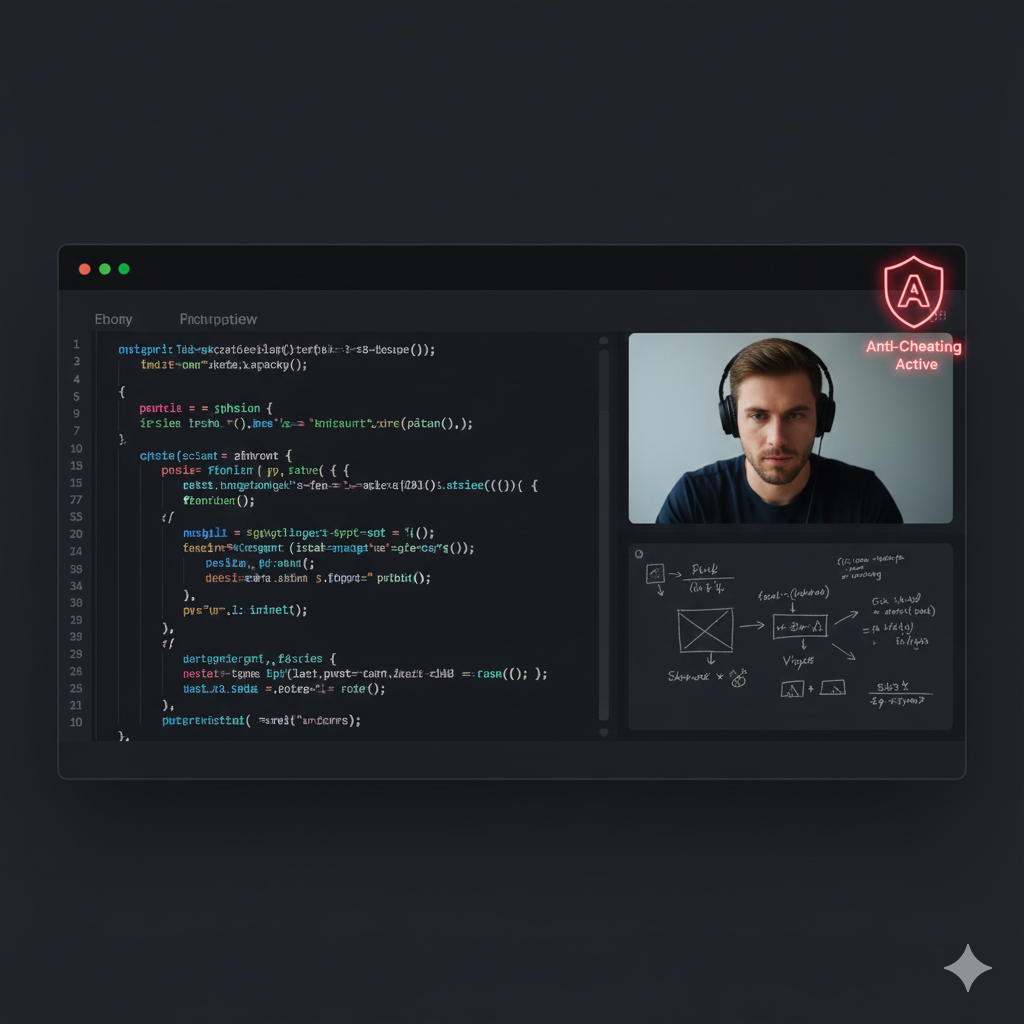
Where IntegrityLens fits
IntegrityLens acts as the identity gate and evidence backbone so candidate identity is stable across the funnel and merges are auditable. It consolidates identity verification and fraud signals into immutable evidence packs that can be written back into the ATS and referenced when records need to merge.
Verify identity in under three minutes before the interview starts, so access is gated on identity state rather than scheduling state.
Use immutable evidence packs with timestamps and reviewer notes to make merges and exceptions audit-ready.
Support step-up verification when fraud signals appear, without stopping the entire funnel.
Keep a single source of truth by writing identity outcomes back into the ATS.
Use zero-retention biometrics to reduce sensitive data persistence while retaining decision evidence.
Anti-patterns that make fraud worse
These practices reliably increase fraud exposure and audit cleanup work because they create unlogged identity changes and irreversible data drift.
Grant interview access before identity is verified, then try to reconcile identities after the fact.
Merge records on fuzzy name matching alone without evidence requirements and a logged approver.
Allow each vendor to mint its own candidate ID without a canonical key and idempotent upsert rules.
Implementation runbook
Implement deterministic identifiers first, then merge governance, then access gating. This ordering reduces duplicates without creating new cycle-time bottlenecks. Every step below includes an SLA, an explicit owner, and what must be logged to remain defensible.
Step 1: Publish Canonical Candidate Key policy. Owner: Security + Recruiting Ops. SLA: 5 business days. Log: policy version and precedence rules.
Step 2: Implement deterministic matching and idempotent upserts across integrations. Owner: Engineering with Recruiting Ops requirements. SLA: 2 sprints. Log: match inputs, idempotency key, and outcome.
Step 3: Stand up merge review queue with escalation. Owner: Recruiting Ops. SLA: 10 business days. Log: reviewer, timestamp, evidence, decision.
Step 4: Gate interview access on identity state. Owner: Security. SLA: 1 sprint. Log: access grant event, expiration, identity snapshot.
Step 5: Daily reconciliation for orphan clusters and fan-out IDs. Owner: Analytics + Recruiting Ops. SLA: daily. Log: run ID, affected records, time-to-merge.
Step 6: Quarterly controls review and bias guardrails. Owner: Compliance + Security. SLA: quarterly. Log: samples reviewed, findings, remediation tickets.
Related Resources
Key takeaways
- Treat duplicate records as identity drift, not just CRM cleanup. The control objective is one candidate identity with one evidence trail.
- Use deterministic identifiers with precedence rules. Email and phone change, documents and biometrics do not.
- Make merges review-bound with SLAs and immutable logs. If it is not logged, it is not defensible.
- Design for retries and reconciliation. Webhooks will arrive out of order and vendors will create partial records.
- Gate interview access on identity, not scheduling. Identity verification before access closes the proxy interview lane.
Use this as the contract between sourcing tools, ATS, and interview platforms. It defines canonical identifiers, merge tiers, SLAs, and what must be written into the immutable event log.
Designed for idempotent upserts, out-of-order webhooks, and an SLA-bound merge review queue.
policyVersion: "2026-04-30"
canonicalCandidateKey:
name: "cck"
generation:
provisional:
method: "uuid-v7"
when: "on_first_seen_in_any_system"
verified:
method: "sha256"
input: "verificationTransactionId"
when: "on_identity_verified"
identifiers:
# Ordered by determinism and audit value
strong:
- name: "verificationTransactionId"
source: "IntegrityLens"
mutable: false
- name: "documentNumberHash"
source: "IntegrityLens"
mutable: false
medium:
- name: "verifiedPhoneE164"
source: "IntegrityLens"
mutable: true
- name: "verifiedEmail"
source: "IntegrityLens"
mutable: true
weak:
- name: "fullName"
source: "ATS_or_CRM"
mutable: true
- name: "linkedinUrl"
source: "CRM"
mutable: true
mergeRules:
autoMerge:
slaMinutes: 15
conditionsAny:
- allMatch: ["verificationTransactionId"]
- allMatch: ["documentNumberHash"]
- allMatch: ["verifiedPhoneE164", "verifiedEmail"]
requireEventLogFields:
- actor: "system"
- timestamp
- idempotencyKey
- matchedIdentifiers
- beforeCandidateIds
- afterCandidateId
reviewMerge:
slaHours: 8
owner: "RecruitingOps"
escalationOwner: "Security"
conditionsAny:
- allMatch: ["verifiedEmail"]
- allMatch: ["verifiedPhoneE164"]
- weakSignals: true
requireEvidence:
- "candidate_confirmation" # email or in-product confirmation
- "verification_snapshot" # current identity state
- "reviewer_note"
prohibitMerge:
conditionsAny:
- conflict: ["documentNumberHash"]
- conflict: ["verificationTransactionId"]
action: "open_fraud_case"
accessGating:
interviewAccess:
default: "deny"
allowWhenIdentityStateIn: ["Verified", "Verified-StepUp"]
tokenExpiryMinutes: 60
logRequired: true
auditLog:
immutability: "append-only"
retentionDays: 365
requiredEvents:
- "candidate.created"
- "candidate.updated"
- "candidate.merge_suggested"
- "candidate.merged"
- "candidate.merge_denied"
- "identity.verified"
- "identity.step_up_requested"
- "interview.access_granted"
- "interview.access_denied"Outcome proof: What changes
Before
Duplicate candidates were discovered late in the process, rubrics were split across profiles, and merge decisions were handled in spreadsheets without a consistent approver trail.
After
A canonical candidate key was introduced with deterministic identifiers. Merges were routed through an SLA-bound review queue, and interview access was gated on verified identity state. Merge decisions and identity outcomes were written into an append-only event log and attached to a single evidence pack per candidate.
Implementation checklist
- Define a canonical Candidate Key and publish it as a shared contract across systems.
- Implement idempotent upsert and merge APIs with deterministic matching rules.
- Add an SLA-bound merge review queue with explicit owners and escalation.
- Write every merge decision into an append-only event log with timestamps, actor, and evidence.
- Require identity verification before interview access for risk-tiered roles.
- Continuously reconcile orphaned records and track time-to-merge as a compliance KPI.
Questions we hear from teams
- What is a deterministic identifier in hiring systems?
- A deterministic identifier is a stable, non-ambiguous key used to link a candidate across tools. It is derived from strong signals like a verification transaction ID or document hash, not from mutable fields like name or unverified email.
- Why are duplicate candidate records a compliance risk?
- Duplicates fragment the evidence trail. When approval, rubrics, and identity assertions are spread across profiles, you cannot reliably prove who approved the hire, what evidence they saw, or whether the interviewed person matches the hired person.
- What should be auto-merged vs manually reviewed?
- Auto-merge only when strong identifiers match, and log the rule and idempotency key. Route anything based on a single medium identifier or weak signals into a review queue with an SLA and an accountable approver.
- How do you keep merges defensible during webhook retries and outages?
- Use idempotent upserts and an append-only event log. Every vendor callback should include an idempotency key so replays do not create new profiles, and every merge should write a before-and-after mapping event with timestamps and actor.
Ready to secure your hiring pipeline?
Let IntegrityLens help you verify identity, stop proxy interviews, and standardize screening from first touch to final offer.
Watch IntegrityLens in action
See how IntegrityLens verifies identity, detects proxy interviewing, and standardizes screening with AI interviews and coding assessments.
