Benchmark Assessment Pass Rates Without Missing Fraud
A COO-grade method to separate real skill gaps from funnel contamination, and to benchmark pass rates for your stack without importing someone else's bias.
A pass rate without cohort, version, and integrity context is not a benchmark. It is a guess with budget impact.Back to all posts
When pass rates collapse two weeks before a headcount deadline
Your quarterly delivery plan depends on filling five backend roles. Two weeks into the sprint, the coding assessment pass rate for "Java + Spring" drops from "normal" to "almost nobody". Hiring managers demand a harder screen to stop AI cheating. Recruiting wants the bar lowered to keep throughput. Security asks whether this is an identity fraud wave. You are the one who has to pick a lever without breaking cycle time or brand. Recommendation: treat a sudden pass-rate shift as an operational incident until proven otherwise. First stabilize measurement (cohorts, versions, sample size), then separate skill signal from integrity signal, then decide whether to tune difficulty or add step-up verification.
What you can do by end of day
You will be able to (1) define stack-specific pass-rate baselines that hold up across quarters, (2) detect assessment drift vs cohort drift vs integrity incidents, and (3) set a step-up policy that preserves speed for low-risk candidates while escalating only the sessions that contaminate your benchmark.
Why "industry standard pass rates" break in real funnels
Recommendation: use external benchmarks only as a loose directional reference and never as a target KPI. Most public "pass rate" numbers blend different seniority bands, different test formats (MCQ, take-home, live), different proctoring, and different candidate sources. If you import them into ops, you create two risks: you tune your assessment to match someone else's applicant mix, and you miss integrity issues because you normalize abnormal behavior as "market conditions". A better operator stance: treat pass rate as a health metric of a specific assessment version run on a specific cohort, with integrity context attached. Then compare like with like.
Checkr reported that 31% of hiring managers said they interviewed someone who later turned out to be using a false identity. Directionally, this means identity risk is not rare and can touch mainstream hiring. It does not prove your org's rate, your tech stack's rate, or that every low pass rate is fraud. https://checkr.com/resources/articles/hiring-hoax-manager-survey-2025
Pindrop stated that 1 in 6 applicants to remote roles showed signs of fraud in one real-world pipeline. Directionally, remote funnels can have meaningful contamination that distorts assessment outcomes. It does not mean 1 in 6 are confirmed fraud, or that on-site roles match that ratio. https://www.pindrop.com/article/why-your-hiring-process-now-cybersecurity-vulnerability/
Ownership, automation, and sources of truth
Recommendation: assign one owner for benchmark definitions, one owner for integrity thresholds, and keep the ATS as the system of record. Who owns what: - Recruiting Ops owns cohort definitions, assessment version control, and reporting cadence. - Security (or a security liaison) owns integrity signal thresholds, step-up triggers, and retention controls. - Hiring managers own rubric alignment for "Day 1" tasks and approve difficulty bands, not ad hoc overrides. What is automated vs manually reviewed: - Automated: identity verification outcomes, integrity risk scoring, assessment telemetry, and queue routing. - Manual: only the step-up review queue, with an SLA and an appeal path for candidates flagged by false positives. Sources of truth: - ATS: candidate stage changes, requisition metadata (stack, level), decision outcomes. - Assessment system: task version, score breakdown, runtime/attempt telemetry. - Verification service: identity verification events and Evidence Packs linked to the ATS record.
How to benchmark pass rates for your tech stack
Recommendation: build internal baselines by stack and level using three layers: cohort hygiene, assessment versioning, and integrity segmentation. Step 1: Define the cohort like an operator, not like a job title. - Stack: e.g., "Node.js + Postgres", "Java + Spring", "Python + Django". - Level band: junior, mid, senior, staff (use your leveling guide, not self-reported years). - Work mode: remote vs hybrid vs on-site. - Source channel: inbound, outbound, referral, agency. This often explains more variance than you expect. Step 2: Lock assessment versioning. - Treat every change to prompts, test cases, or time limits as a new version. - Maintain difficulty bands (A, B, C) based on rubric outcomes from known-good employees or past hires. Step 3: Set minimum sample sizes before declaring a "trend". - Small cohorts swing wildly. If you cannot meet a minimum N, widen the time window or merge only truly comparable roles. Step 4: Add integrity segmentation to your pass-rate dashboard. - Compare pass rate for "verified low-risk" vs "unverified or stepped-up" sessions. If the gap is large, you likely have funnel contamination or a review policy issue. Step 5: Compare against external benchmarks only after the above. - If your internal baseline is stable and your process is instrumented, then external references can help you ask: "Are we unusually strict for this stack?" not "What should our KPI be?"

Pass rate by stack-level-version (primary)
Median time-to-complete by version (detects coaching and content leaks)
Re-attempt rate and device reuse rate (detects farming)
Step-up rate and step-up fail rate (detects policy tuning issues)
Offer-to-start quality notes tied to assessment outcomes (validates predictive value)
Which integrity signals keep your benchmarks honest
Recommendation: use integrity signals to explain variance, not to auto-reject by default. Benchmarks get distorted when a subset of candidates are not the same "unit" you think you are measuring, for example a proxy test-taker, a deepfake interview, or a candidate using prohibited real-time assistance. Integrity signals let you segment and step up without torching good candidates. Practical signals that map to operations: - Identity mismatch risk: document, face, and voice inconsistencies across steps. - Session anomalies: multiple candidates from the same device fingerprint, impossible completion times, repeated identical solution structure across accounts. - Environment risk: suspicious network patterns that correlate with fraudulent activity (use as a step-up trigger, not a conviction). Operator note: integrity signals become useful only when they feed a policy. A dashboard without routing just creates anxiety.
A step-up policy that protects speed and reduces false positives
Recommendation: adopt Risk-Tiered Verification so low-risk candidates flow fast while high-risk sessions generate Evidence Packs for review. A workable flow for COOs is: default to fast verification and assessments, then step up only when you see anomaly clusters that threaten benchmark integrity or decision quality. Step-by-step:
Baseline verification before the interview starts: verify identity early so assessment outcomes map to a real person.
Define step-up triggers tied to benchmark contamination: e.g., sudden pass-rate spike or collapse within a cohort, high device reuse, or repeated near-identical submissions.
Route to a review queue with an SLA: keep reviewer fatigue under control by reviewing only top-risk bands.
Decide outcomes with an appeal path: "clear", "retest", or "disqualify" should be logged with reasons, not vibes.
Run monthly drift reviews: if step-up rate grows, either your triggers are too sensitive or attackers are adapting. Tune it like you tune any control.
stack-level pass-rate benchmark with integrity segmentation
This query is designed for Recruiting Ops to run monthly. It creates a benchmark table by tech stack, level, and assessment version, segmented by verification tier so you can see whether integrity controls are affecting throughput or data quality.
Anti-patterns that make fraud worse
Recommendation: remove these three behaviors first, because they directly increase funnel contamination and distort your benchmarks.

Publishing a single blended pass rate in exec dashboards without cohort and version breakdowns, which pressures teams into ad hoc bar changes.
Zero-tolerance auto-reject rules on weak signals (for example, one anomaly) that push good candidates away and train fraudsters to probe your thresholds.
Allowing assessment changes without versioning and back-testing, which makes every quarter look like a different market instead of a different test.
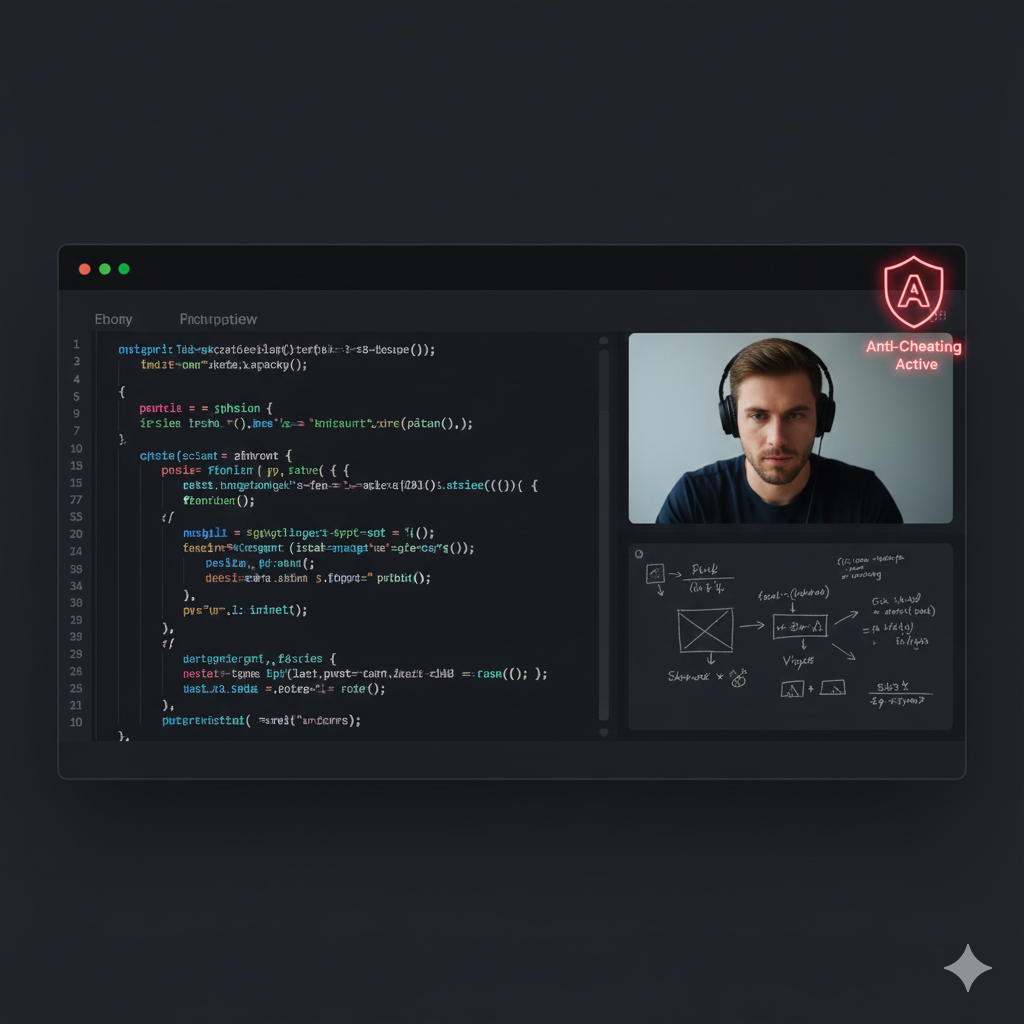
Where IntegrityLens fits
IntegrityLens AI helps you benchmark pass rates you can trust by keeping the hiring workflow and integrity signals in one defensible pipeline. It combines an ATS with biometric identity verification, fraud detection, AI screening interviews, and coding assessments so your benchmarks are tied to the same candidate record, not scattered across tools. Used by TA leaders, recruiting ops teams, and CISOs to reduce funnel leakage and create audit-ready decisions. - ATS workflow from source to offer with consistent stage data - Identity verification in 2-3 minutes (document + voice + face) before interviews - Risk-tiered fraud detection with Evidence Packs for exceptions - 24/7 AI screening interviews to stabilize early-stage filtering - Coding assessments supporting 40+ languages with versionable tasks
Operator takeaways for COOs
Recommendation: treat pass-rate benchmarking as an operational control, not a recruiting vanity metric. If your pass rate is low but stable for a well-defined cohort and version, that is usually a calibration choice. If it is unstable or diverges sharply by verification tier, that is a process integrity problem or a cohort drift problem. Make the dashboard show which one. Finally, avoid setting pass-rate KPIs without also tracking candidate experience and downstream hiring quality. The goal is signal-to-noise, not maximum rejection throughput.
Sources
- Checkr, Hiring Hoax (Manager Survey, 2025): https://checkr.com/resources/articles/hiring-hoax-manager-survey-2025
Pindrop, Why your hiring process is now a cybersecurity vulnerability: https://www.pindrop.com/article/why-your-hiring-process-now-cybersecurity-vulnerability/
Key takeaways
- Benchmark against your own cohorts first, then use industry benchmarks only as directional guardrails.
- A single blended pass rate is not a metric, it is a hiding place. Segment by stack, seniority, and assessment version.
- Integrity signals explain pass-rate variance and reduce false conclusions like "the test got harder" or "the market is worse".
- Use risk-tiered step-ups (not zero tolerance) so high-signal anomalies get reviewed without tanking candidate throughput.
- Operational ownership and sources of truth prevent shadow spreadsheets and inconsistent overrides.
Run monthly to create a cohort-consistent baseline by tech stack, level, and assessment version.
Segment by verification tier so you can detect benchmark contamination and policy side effects.
Assumes you store assessment events and verification outcomes keyed to the ATS candidate_id.
-- Benchmark pass rates by stack/level/version, segmented by verification tier
-- Replace table and column names to match your warehouse.
WITH cohort AS (
SELECT
c.candidate_id,
r.req_id,
r.tech_stack, -- e.g., 'java-spring'
r.level_band, -- e.g., 'mid'
r.work_mode, -- 'remote' | 'hybrid' | 'onsite'
c.source_channel, -- 'inbound' | 'outbound' | 'referral' | 'agency'
a.assessment_version,
a.score_pct,
a.passed,
a.completed_at::date AS completed_date
FROM ats_candidates c
JOIN ats_reqs r ON r.req_id = c.req_id
JOIN assessment_runs a ON a.candidate_id = c.candidate_id
WHERE a.completed_at >= date_trunc('month', current_date) - interval '6 months'
AND a.status = 'completed'
), verification AS (
SELECT
v.candidate_id,
-- Example tiers: 'verified-low', 'verified-step-up', 'unverified'
CASE
WHEN v.verification_status = 'verified' AND v.risk_tier = 'low' THEN 'verified-low'
WHEN v.verification_status = 'verified' AND v.risk_tier IN ('medium','high') THEN 'verified-step-up'
ELSE 'unverified'
END AS verification_tier,
v.latest_decision_at
FROM identity_verifications v
QUALIFY row_number() OVER (PARTITION BY v.candidate_id ORDER BY v.latest_decision_at DESC) = 1
)
SELECT
co.tech_stack,
co.level_band,
co.assessment_version,
co.work_mode,
co.source_channel,
ver.verification_tier,
count(*) AS attempts,
avg(CASE WHEN co.passed THEN 1.0 ELSE 0.0 END) AS pass_rate,
percentile_cont(0.50) WITHIN GROUP (ORDER BY co.score_pct) AS median_score_pct
FROM cohort co
LEFT JOIN verification ver ON ver.candidate_id = co.candidate_id
GROUP BY 1,2,3,4,5,6
HAVING count(*) >= 25 -- operator guardrail: avoid tiny samples
ORDER BY tech_stack, level_band, assessment_version, verification_tier;Outcome proof: What changes
Before
Exec reviews were driven by a single blended assessment pass rate. Teams reacted by changing difficulty and adding manual checks, creating reviewer fatigue and inconsistent exceptions.
After
Recruiting Ops published stack-level-version baselines segmented by verification tier, with a step-up queue owned jointly with Security. Hiring managers aligned assessments to "Day 1" tasks and stopped ad hoc bar changes.
Implementation checklist
- Define the cohort: role family, level, location/remote, and required stack.
- Lock assessment versioning and difficulty bands before comparing periods.
- Track pass rates with confidence intervals and minimum sample sizes.
- Add integrity segmentation: verified vs unverified, high-risk vs low-risk sessions.
- Set step-up thresholds and reviewer SLAs to prevent backlog and reviewer fatigue.
- Publish a monthly "assessment health" report with drift flags and root-cause notes.
Questions we hear from teams
- What is a "good" pass rate for a Java, Python, or Node role?
- A "good" pass rate is the rate that stays stable for your stack-level-version cohort and correlates with downstream interview performance. External numbers can be directionally informative, but they rarely match your source mix, seniority distribution, or proctoring rules.
- How do integrity controls affect pass-rate benchmarks?
- Integrity controls change who is included in the measured population. The operational fix is to segment metrics by verification tier and track step-up rates, so you can see whether changes are improving data quality or creating unnecessary friction.
- Should we lower the bar if pass rates are too low?
- Only after you verify that the cohort and assessment version are stable and that integrity segmentation is not showing contamination. If the low rate is stable and your rubric matches "Day 1" tasks, lowering the bar may increase downstream interview cost and hiring risk.
- How do we avoid rejecting strong candidates due to false positives?
- Use step-up verification and retest paths instead of auto-reject. Keep triggers explicit, log decisions in the ATS, and measure false positive rates by reviewing outcomes from the step-up queue.
Ready to secure your hiring pipeline?
Let IntegrityLens help you verify identity, stop proxy interviews, and standardize screening from first touch to final offer.
Watch IntegrityLens in action
See how IntegrityLens verifies identity, detects proxy interviewing, and standardizes screening with AI interviews and coding assessments.
